AWS Shared Responsibility Model

Security and compliance are shared responsibilities between AWS and the customer.
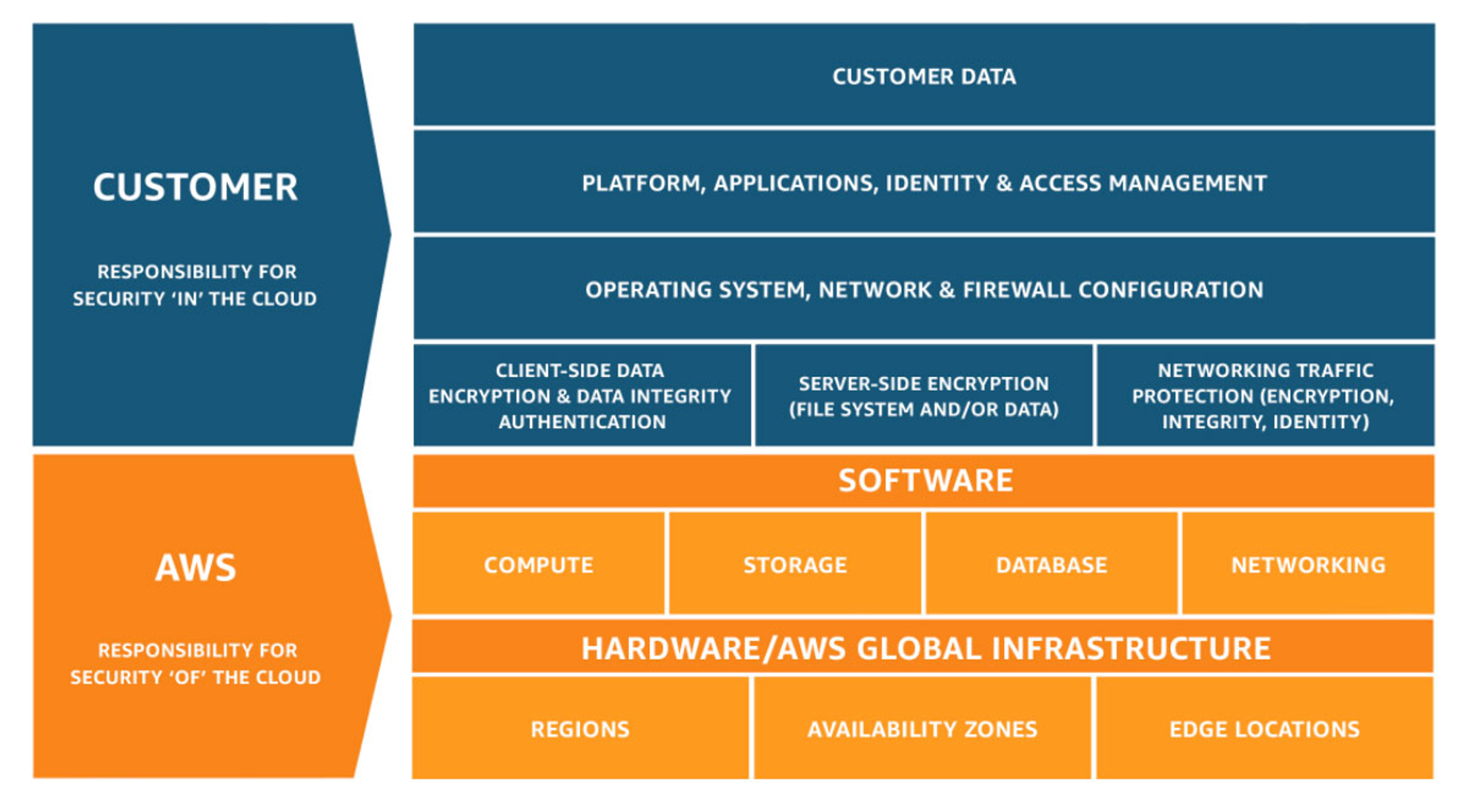
⚡ AWS responsibility “Security of the Cloud” AWS is responsible for protecting the infrastructure that runs all of the services offered in the AWS Cloud. This infrastructure is composed of the hardware, software, networking, and facilities that run AWS Cloud services.
⚡ Customer responsibility “Security in the Cloud” Customer responsibility will be determined by the AWS Cloud services that a customer selects. This determines the amount of configuration work the customer must perform as part of their security responsibilities.
Below are examples of controls managed by AWS, AWS Customers and/or both.
Inherited Controls – Controls that a customer fully inherits from AWS.
- Physical and Environmental controls
Shared Controls – Controls that apply to the infrastructure and customer layers but in completely separate contexts or perspectives. In shared control, AWS provides the requirements for the infrastructure, and the customer must provide their own control implementation within their use of AWS services. Examples include:
Patch Management – AWS is responsible for patching and fixing flaws within the infrastructure, but customers are responsible for patching their guest OS and applications.
Configuration Management – AWS maintains the configuration of its infrastructure devices, but a customer is responsible for configuring their own guest operating systems, databases, and applications.
Awareness & Training - AWS trains AWS employees, but customers must train their employees.
Customer Specific – Controls solely the customer's responsibility based on the application they are deploying within AWS services. Examples include:
- Service and Communications Protection or Zone Security may require customers to route or zone data within specific security environments.
Can you do this yourself in the AWS Management Console?
If yes, you are likely responsible.
- Security groups, IAM users, patching EC2 operating systems, patching databases running on EC2, etc.
If not, AWS is likely responsible for managing data centers, security cameras, cabling, patching RDS operating systems, etc.
Encryption is a shared responsibility.